Seasonal Kik Spam Messages
One constant theme when it comes to spam is that it tries to co-ordinate with current events, in order to increase the chance that it will be acted upon. These current events can be topical news events or known upcoming holiday/seasonal or sports events. This behaviour is seen on any types of messaging bearers that experiences spam. In the last few months there have been a series of spam campaigns in the shape of picture messages being sent on Kik messenger that have shown very strong seasonal attributes, and are worth reviewing.
The sequence of Kik picture spam messages we have collected in the last 2 months is as follows:





In order, these were received on:
- Halloween: Amazon
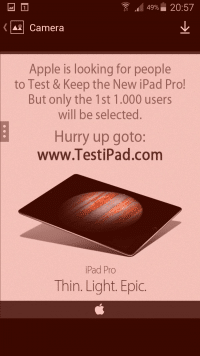
- Early Nov: iPad
- Mid Nov: iTunes
- Thanksgiving: McDonalds
- Cyber Monday: BestBuy
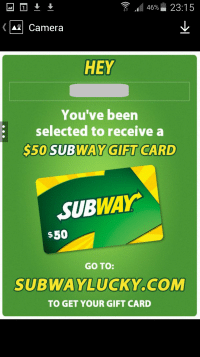
- Dec 7th,18th: Subway
- Christmas Day: Wendy’s
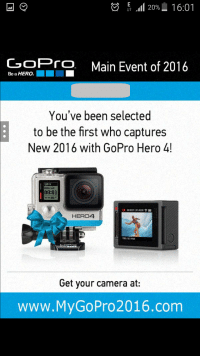
- New Year’s Day: GoPro
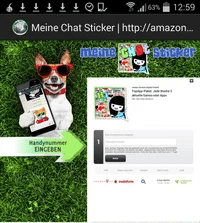
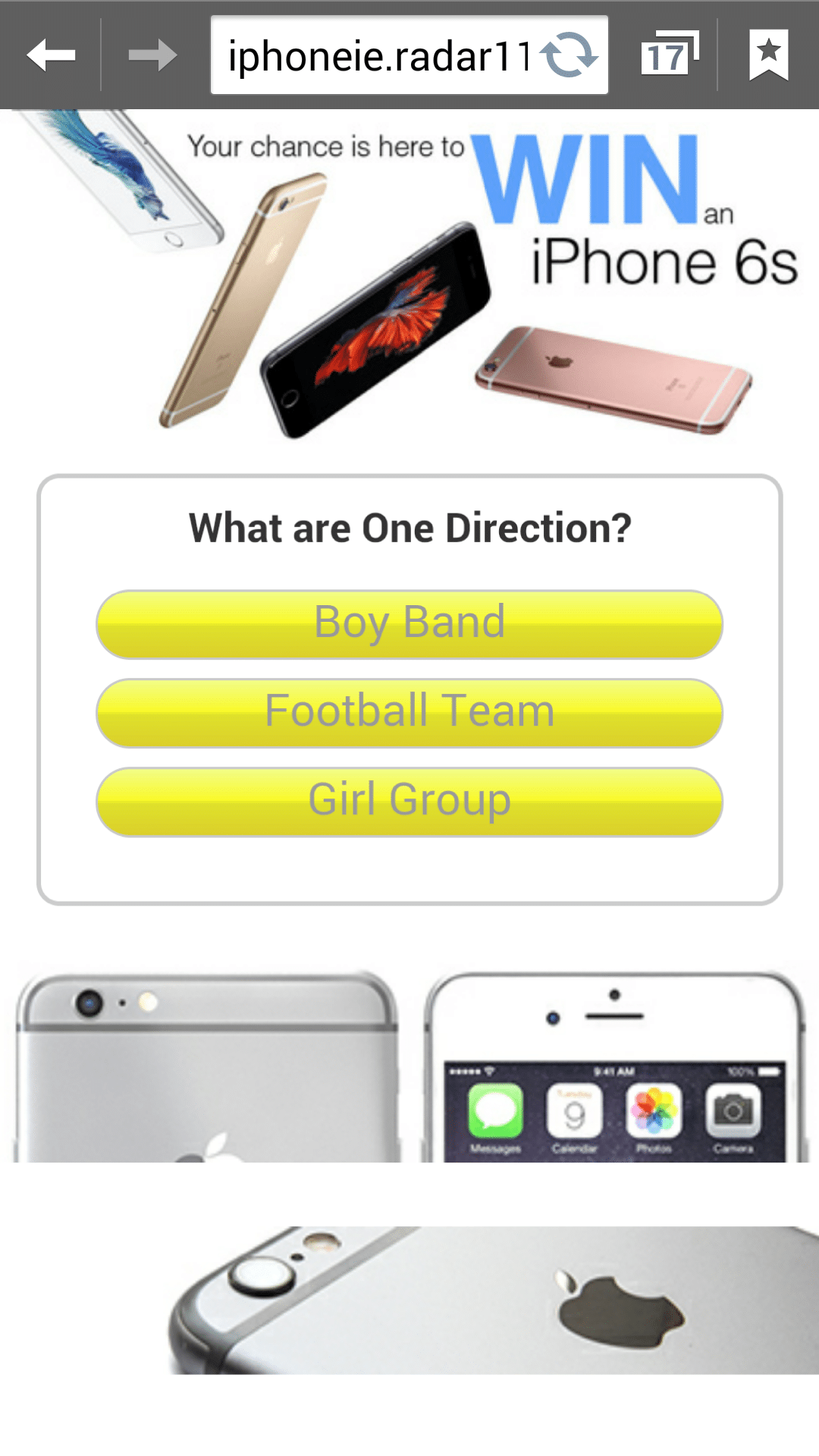
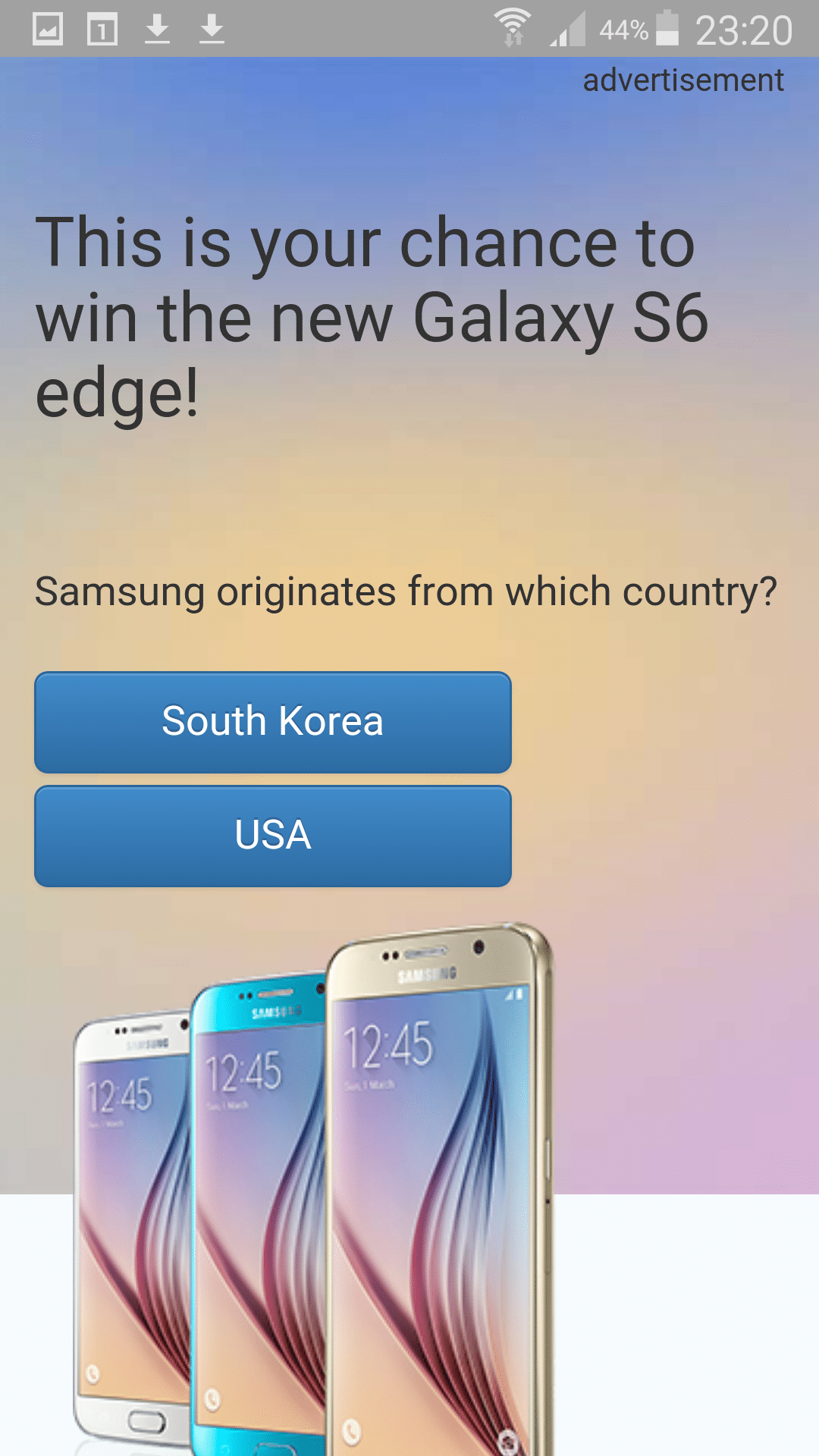
You can see that the spam attack involves a picture message that uses a well-known brand, in order to encourage the recipient of the spam to go to the link. The link needs to be easily memorable as it is not normally possible for the spam receiver to click on a link received on a Kik picture message. You can also see that picture spam is not only tied to holiday events, but can be sent on other periods as well. Once a link is clicked, the spam recipient is taken to a webpage that is dependent on their bowser location, but are typically given a screen that encourages them to click and answer a question to win a ‘prize’, and sign up to receive message, costing the recipient money. some example screens that the user is given are below:
This geolocation of pages tactic is normally used to get a maximum reach of spam, and to allow the spammers to deliver advertising for multiple ‘customers’.
Another interesting fact is that this attack is very consistent, and many more brands that the above have been involved. All of the original URLs contained in the Kik image spam resolve to a Russian IP address, and if we examine this IP’s activity we can see that, as well as the above brands,this IP address has potentially been involved with many more brand attacks using: Samsung, Foot Locker, Walmart, fitbit, Sony, Sixflags, Starbucks, Popeyes, Kohl, Home Depot, Uber, HP, Kroger & Chipotle. The date of registration is also interesting. Sometimes the Kik spam is sent out in advance of the domain being registered, either by mistake or more likely to generate demand. This occurred with the Subway attack where a spam message with the domain was received on the 7th of December, but the domain was only created on the 15th – this also coincided with another spam attack received a few days later. Other times the URL is created immediate prior to the spam attack – such as the most recent GoPro attack. This domain was created on the 31st, and the spam message containing the domain received on the 1st of January 2016.

While not very technically sophisticated, the effort that goes into creating the individual picture messages & obtaining easily memorable web pages per holiday event is indicative of a specialist, determined effort – as well as the continued attraction of co-ordinating spam with holiday period. In effect this type of spam indicates a widening of the spam activity on Kik, which up to now has normally been of the adult type but which is still on-going. Its also highly probable than this Brand spam trend will continue for the foreseeable future, meaning that Kik users are likely to continued to be targeted by this picture spammer.
In the meantime, and as always, when receiving an unsolicited message do not respond, click on, or go to any link if you are uncertain of its source, and have a Happy (and safe) New Year!